In an age where cyber threats loom at every corner of the digital landscape, securing your network is not just an option. It’s a necessity.
For you as an IT professional, developing and maintaining a robust network security strategy is paramount. The challenge, however, lies in knowing where to start and what measures are truly essential.
Table of contents:
What is Network Security?
Network security consists of software, hardware configurations, and policies that work together to protect against potential attacks.
Why is Network Security Important?
Network security is essential because it safeguards an organization’s data integrity. It also protects confidentiality and availability from cyber threats like hackers and malware.
Additionally, robust network security ensures smooth business operations, maintains stakeholder trust and helps comply with regulatory standards.
To sum up, effective network security is fundamental to all kinds of organizational infrastructure.
Going on, you can read more about each of the network security checklist components:
#1 Establish a Comprehensive Network Map
| Action: | Create a detailed inventory of all network-based devices, including routers, PDUs, switches, firewalls, and endpoints. |
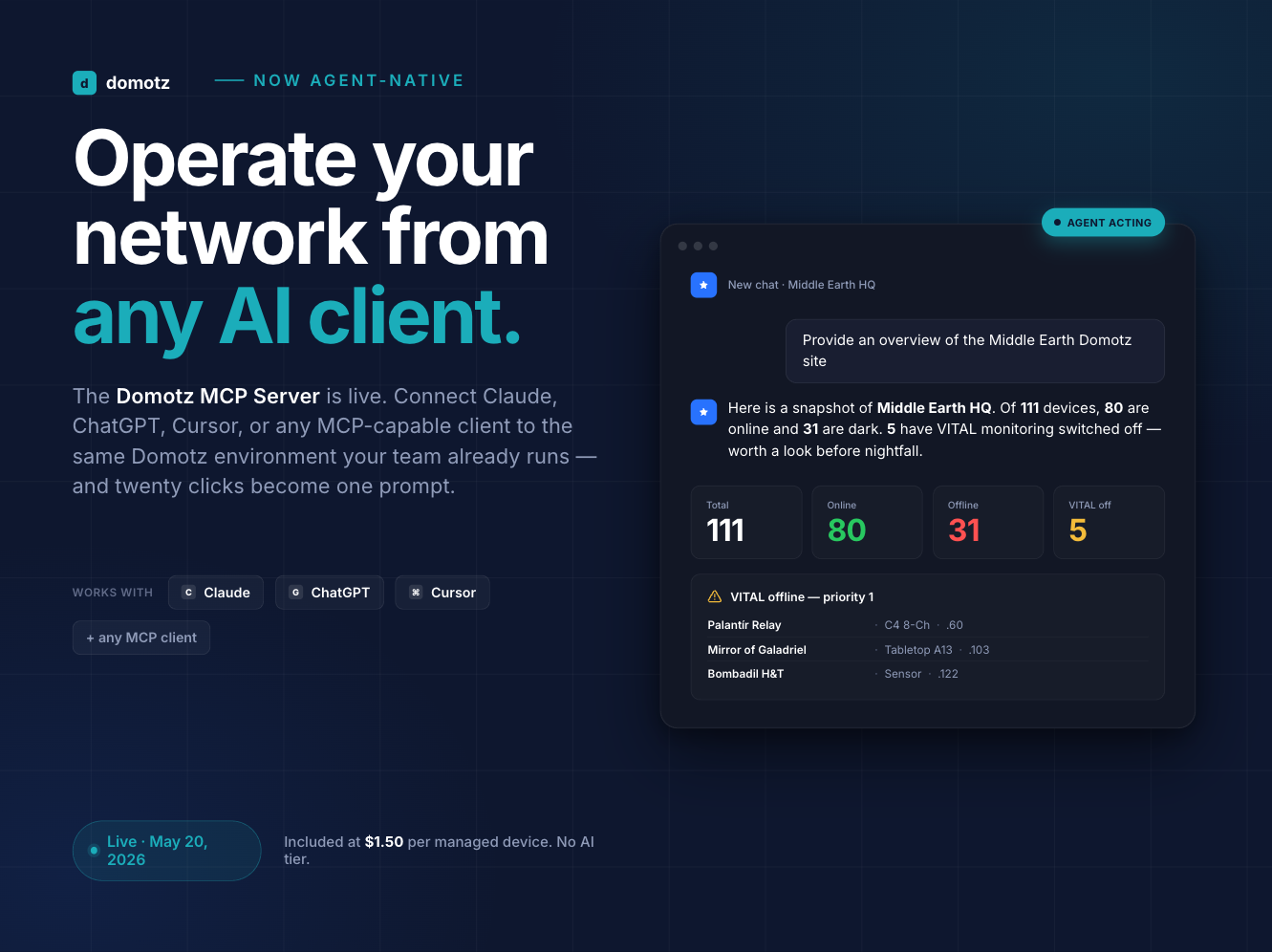
| How Domotz Can Help: | Leverage Domotz to automatically discover and map all IP-connected devices on the network. You can rely on full visibility and control of the networks you manage. Use our asset discovery and classification feature to quickly and easily discover network-based assets across all your networks, associated VLANs, and subnets. Domotz also offers a network topology mapping feature, which provides a graphical representation of how devices are connected to each other on the network. |
#2 Implement Strong Access Controls
| Action: | Ensure only authorized personnel can access sensitive information. |
| How Domotz Can Help: | Rely on Domotz to ensure that individuals only access the information and tools necessary for their roles. |
#3 Perform Regular Software Updates and Configurations Management
| Action: | Keep all network devices and software up to date with the latest security patches and firmware updates. |
| How Domotz Can Help: | Domotz’s monitoring capabilities include alerts for new firmware updates and potential vulnerabilities. You can rely on our backup and restore network configurations for switches, firewalls, and access points and get alerts about changes. Check out our backup control and configuration management integrations. Our software can also help you backup and restore network configurations for switches, firewalls, and access points and get alerts about changes. Check out our backup control and configuration management integrations. |
#4 Secure and Monitor Network Endpoints
| Action: | Implement endpoint protection solutions and monitor endpoints for suspicious activities. |
| How Domotz Can Help: | Domotz provides detailed monitoring of any network endpoint, including activity logs and real-time alerts for unusual behavior, aiding in the rapid detection and response to potential threats. In other words, Domotz can help you with network management by offering secure remote connections, SNMP sensors, TCP services, and custom integrations. These enable teams to work smarter and faster by continuously monitoring and logging data from all connected devices. |
#5 Utilize Advanced Encryption Techniques
| Action: | Apply strong encryption standards for data at rest and in transit to protect sensitive information. |
| How Domotz Can Help: | While Domotz itself ensures encrypted communication between its agents and the cloud, it also provides insights into the encryption status of devices and traffic, helping identify areas where encryption needs to be strengthened. |
#6 Implement a Secure Network Architecture
| Action: | Design the network with security in mind, including the use of firewalls, segmentation, and VPNs for remote access. |
| How Domotz Can Help: | Domotz supports network segmentation efforts by providing visibility into network traffic and device connectivity, facilitating the identification and isolation of segments. Check our network performance and security features. |
#7 Regularly Conduct Vulnerability Assessments
| Action: | Perform routine network scans to identify and address vulnerabilities before they can be exploited. |
| How Domotz Can Help: | Domotz can significantly aid in conducting regular vulnerability assessments by providing tools that continuously scan and monitor network devices for potential security threats. It alerts users to unusual activity and insecure configurations, enabling IT teams to address vulnerabilities promptly. Additionally, Domotz’s ability to integrate with various security vulnerability scanners means that assessments can be comprehensive and tailored to specific network needs, enhancing overall cybersecurity posture. |
#8 Monitor for Suspicious Network Traffic
| Action: | Use network monitoring tools to detect unusual traffic patterns or unauthorized access attempts. |
| How Domotz Can Help: | Domotz’s continuous monitoring and alerting capabilities enable the detection of anomalous traffic and potential security breaches, facilitating quick mitigation actions. |
#9 Develop and Test Incident Response Plans
| Action: | Establish a detailed cybersecurity incident response plan and conduct regular drills to test the organization’s readiness. |
| How Domotz Can Help: | Domotz can be part of an incident response strategy by providing the necessary network insights and device access control to identify and isolate affected systems quickly. |
#10 Educate Staff on Cybersecurity Best Practices
| Action: | Regularly train employees on the importance of cybersecurity and how to recognize potential threats. |
| How Domotz Helps: | While Domotz focuses on network monitoring and management, it contributes to cybersecurity awareness by highlighting the importance of network hygiene and enabling IT teams to share insights on network health and security posture with the wider organization. |
Conclusion
Implementing these measures will significantly enhance an organization’s network security posture. Domotz’s capabilities in network monitoring, device management, and security compliance play a pivotal role in supporting these essential security measures.
Further reading: